Getting The Data Protection To Work
Wiki Article
An Unbiased View of Aws Cloud Backup
Table of ContentsAn Unbiased View of Ransomware ProtectionHow Aws Backup can Save You Time, Stress, and Money.An Unbiased View of Protection Against RansomwareWhat Does Rto Do?Some Known Incorrect Statements About Rto The 10-Minute Rule for Aws Cloud Backup

International authorities have actually tipped in with governing compliance like General Data Protection Law (GDPR). The GDPR stresses the personal information rights of EU homeowners, including the right to alter, accessibility, eliminate, or transfer their information. Personal data refers to any info that associates with a person. This consists of names, physical traits, addresses, racial or ethnic qualities, and biometric information like DNA and finger prints.
To keep their information offered in all times, companies require to maintain the IT infrastructure active even in the case of a calamity. This state of guaranteed access to information is referred to as data schedule. This post evaluates the basics of data schedule as well as its obstacles, and uses techniques to keep a high degree of data schedule.
Without a correct information protection plan, delicate info can drop into the hands of enemies, allowing them to acquire accessibility to your network, and also reveal the individual information of customers and employees. This article introduces the idea of information safety and security and the various devices as well as approaches you can utilize to shield your information as well as protect against a catastrophe.
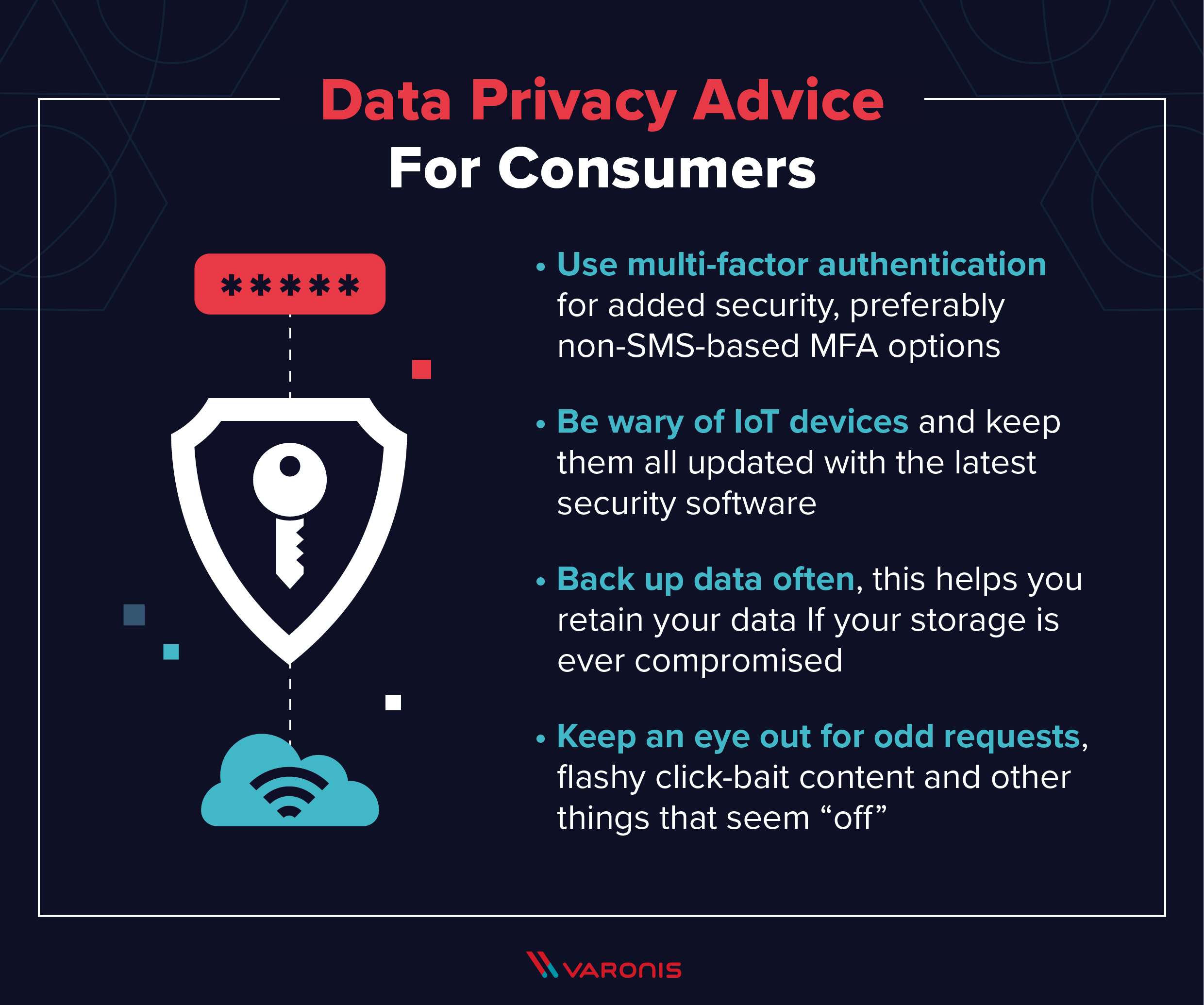
Not known Facts About Ec2 Backup
The encoded details can only be decoded with a distinct decryption secret. You can generate the key either at the time of security or in advance. File encryption makes sure the stability of information by shielding it from unapproved modification. Security reduces the threat of accessing data from undependable resources by verifying information's source.A constant information security system maintains a document of all information changes as well as enables you to restore a system to any type of previous factor in time. This type of backup addresses the problem of losing information developed between 2 scheduled backups. It likewise provides security versus attacks like ransomware or malware, in addition to unintentional removal of information.
Any business that processes as well as shops individual data of EU people, also if it is not physically located in the EU, need to put on the GDPR guidelines. There are 2 main roles in the GDPR: the GDPR Data Processor is an entity that holds or processes this type of data in behalf of one more company, as well as a GDPR Data Controller that gathers or processes personal data for its own objectives.
Object Lock prevents item variation removal throughout a user-defined retention period. Immutable S3 objects are secured utilizing item, or bucket-level configuration of WORM and retention attributes. This functionality provides both information security, including additional protection against unexpected or harmful deletion as well as ransomware and regulatory conformity. Find out more: S3 Things Lock Protecting Information for Ransomware Hazards and Compliance The cloud-based subscription of Workplace 365 allows workers to work anywhere, anytime without the requirement to organize their own material and emails.
The Single Strategy To Use For Rto
Data security is the procedure of guarding important information from corruption, compromise or loss. The importance of data defense increases as the amount of data produced as well as kept remains to grow at unmatched rates. There is likewise little tolerance for downtime that can make it impossible to accessibility important info.
The vital concepts of information defense are to guard and also make available data under all conditions. The term information defense defines both the functional back-up of information in addition to service continuity/disaster recuperation (BCDR). Data defense methods are advancing along 2 lines: data schedule and also information monitoring. Information availability guarantees users have the information they require to conduct company even if the information is harmed or shed.
Aws Cloud Backup for Dummies
Data lifecycle management is the procedure of automating the activity of vital information to online and offline storage space. Details lifecycle monitoring is an extensive strategy for valuing, cataloging and safeguarding information assets from application and individual mistakes, malware and also virus assaults, machine failure or facility interruptions and also disruptions. A lot more lately, data administration has involved include locating ways to open company value from or else inactive duplicates of information for coverage, test/dev enablement, analytics and other purposes.(CDP) backs up all the data in a business whenever a change is made. Information portability-- the capacity to move data amongst various application navigate to these guys programs, computing settings or cloud services-- presents one more collection of problems as well as remedies for information protection.
The smart Trick of Rto That Nobody is Discussing
Information defense is the procedure of guarding crucial info from corruption, compromise or loss. The value of data security enhances as the amount of information produced and stored remains to grow at unprecedented rates. There is also little resistance for downtime that can make it impossible to accessibility essential details (https://sites.google.com/view/clumi0/home).Securing data from concession and also guaranteeing data personal privacy are other crucial components of information security. The coronavirus pandemic triggered countless employees to function from home, leading to the need for remote data defense. Services should adjust to guarantee they are protecting information anywhere staff members are, from a central data facility in the office to laptops in the house.
The key concepts of information protection are to protect as well as make available data under all conditions - https://www.flickr.com/people/196884117@N06/.
Info lifecycle management is an extensive strategy for valuing, cataloging and also securing information properties from application as well as user mistakes, malware and virus strikes, maker failure or center interruptions and disturbances. Much more recently, data monitoring has actually come to consist of locating methods to unlock company worth from or else dormant duplicates of information for reporting, test/dev enablement, analytics and also other purposes.
The Greatest Guide To Ec2 Backup
(CDP) backs up all the information in an enterprise whenever a modification is made. Data transportability-- the capability to relocate data amongst various application programs, computing settings or cloud solutions-- presents an additional collection of issues and also services for information protection.Report this wiki page